Private State Tokens in Online Antifraud: What They Change and Where They Fit
Published on: 2026-04-06 12:35:06
Why Private State Tokens matter
Online antifraud has a problem. The usual signals are weaker than they used to be. Third-party cookies are disappearing. Browsers reduce the fingerprinting surface. VPNs, relay services, and shared devices make location and device checks less reliable. Private State Tokens are one response to that shift.
They give sites a way to verify trust signals without exposing personal data. That matters for lending, ecommerce, and any workflow where you need to decide if a user is real, persistent, and low risk. The goal is not to identify a person by name. The goal is to create a deterministic trust signal that can feed decision logic.
For teams building antifraud rules, that is useful. It adds another input to the ruleset, alongside device data, email signals, behavioral events, and transaction history. Used well, it can reduce false positives and improve review quality.
What Private State Tokens are
Private State Tokens are a browser-based mechanism for transferring a limited trust signal between sites. A site that has observed legitimate user behavior can issue a token. Later, another site can ask whether the browser holds tokens from issuers it trusts.
The key point is privacy. The token is not a personal profile. It is not a tracking cookie. It is a cryptographic signal that can support anonymous verification under defined rules.
That makes it different from traditional fingerprinting. Fingerprinting tries to infer identity from browser and device characteristics. Private State Tokens reduce the need for that approach by giving decision systems a cleaner signal to evaluate.
How the flow works
A common pattern looks like this:
- A user interacts with a site in ways that indicate legitimate behavior.
- The site issues a token through the browser API.
- The token is stored in the browser in a privacy-preserving form.
- Later, a different site asks whether the browser holds valid tokens from trusted issuers.
- If the browser has them, the requesting site can redeem or verify the signal.
- The receiving site uses that result as one input in its decision logic.
This is not a standalone identity system. It is a trust input. That distinction matters. You should not use it as a single approval trigger. You should use it as part of a broader decision flow that also checks fraud rules, product policy, and risk thresholds.
Where it fits in online antifraud
Private State Tokens fit best where you need to answer one question: is this browser connected to a legitimate history from a trusted source?
1. New account opening
Account creation is a common fraud target. Bots create fake accounts, test stolen data, and probe weak onboarding flows. A Private State Token signal can help separate a browser with real purchase history from a fresh, suspicious session.
In practice, that signal can lower friction for low-risk users and send uncertain cases to step-up verification. It should not replace email checks, device intelligence, IP reputation, or velocity rules. It should sit beside them.
2. Loan applications
In lending, the value is in reducing fraud loss without blocking legitimate applicants. A lender can use the token result as one factor in underwriting or fraud screening. If the browser has trusted history, the application may move forward with less friction. If it does not, the flow can ask for stronger proof.
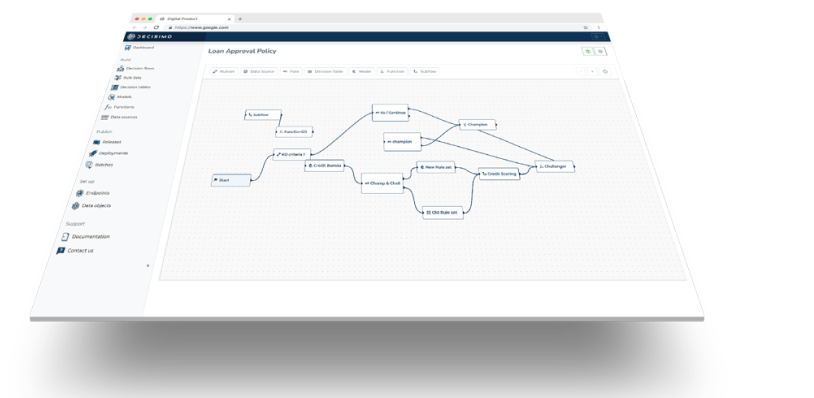
This is especially useful when the lender already uses rule-based decisioning. The token can become a condition in the ruleset, such as: if trusted browser signal is present, and device risk is low, and identity checks pass, then continue automated review. That is deterministic and auditable.
3. Ecommerce checkout
Ecommerce teams can use the signal to identify suspicious carts, account takeover attempts, and payment abuse. A browser with no trusted history is not bad by default. But when that signal appears alongside velocity spikes, mismatched shipping data, or risky payment patterns, it can justify review or decline.
This is where the token helps most. It improves confidence in the decision without exposing more personal data than necessary.
What it can and cannot tell you
Private State Tokens are useful because they are narrow. They tell you something about trusted browser history. They do not tell you everything.
They can help you:
- Detect whether a browser has a trusted prior interaction.
- Reduce reliance on brittle fingerprinting signals.
- Improve risk triage in onboarding and checkout.
- Support step-up decisions in rule engines.
They cannot tell you:
- Whether a user is creditworthy on their own.
- Whether a transaction is safe without other checks.
- Whether a browser session is free from all fraud risk.
- Whether a person should be approved without policy review.
That limitation is a strength. Good antifraud systems use bounded signals. They do not pretend one signal solves the entire problem.
Using the signal in lending decisions
If you work in lending, the token signal can support three areas of decisioning.
Verify identity confidence
A trusted browser history can support the view that the applicant is a real user, not a scripted actor or disposable account. That does not prove identity by itself. It does add weight to the case when other signals also look clean.
Adjust fraud risk
You can assign the token result to a fraud score or a ruleset branch. For example, a trusted token may reduce the likelihood of manual review. No token, or an invalid redemption, may push the case into a stricter path.
Support offer design
Once the applicant clears fraud checks, you can use broader behavioral data to shape offers. That should stay within policy and privacy constraints. The point is not to infer personal traits. The point is to use risk data responsibly inside your decision logic.
Using the signal in ecommerce antifraud
For ecommerce teams, Private State Tokens are most useful when combined with other fraud controls.
Flag high-risk sessions
If the token is missing and the session also shows high velocity, a mismatched device pattern, or an unusual checkout path, the case deserves more scrutiny. The token is one signal among many. The decision comes from the full rule set.
Support account takeover detection
Account takeover often looks like a familiar login from a strange context. Browser trust history can help separate a legitimate returning user from automation or a hijacked session. That is especially useful when paired with login behavior and recovery-event history.
Reduce false positives
One practical benefit is lower friction for good users. When a customer has a trusted browser signal and no other risk markers, the system can avoid unnecessary step-up checks. That improves conversion and reduces support load.
How to use Private State Tokens in a decision engine
If your team uses a decision engine, treat the token as an external data source. Do not hard-code assumptions into application code. Model the signal in rules.
A simple pattern is:
- Check token presence.
- Verify issuer trust.
- Validate redemption response.
- Combine the result with device, email, IP, and behavioral checks.
- Route the case to approve, review, or decline.
That keeps the logic explainable. It also makes policy changes easier. If you decide later that only certain issuers count for certain products, you can update the ruleset without rebuilding the flow.
For teams already using basic rules or scorecards, this fits naturally. The token becomes a structured input with a clear weight and a clear outcome.
Operational and compliance notes
Privacy-preserving does not mean risk-free. You still need to define how you store token results, who can query them, and how long you retain them. You also need to document the role the signal plays in decisioning.
From a governance view, that means three things:
- Keep the rule versioned.
- Log the token check in the decision trace.
- Separate the trust signal from personal data wherever possible.
That gives your risk and compliance teams something they can audit. It also helps you answer a basic question: why was this case approved, reviewed, or declined?
Practical rollout advice
Start small. Add the signal to one decision flow, not every flow. Measure the impact on approval rates, manual review rates, fraud loss, and false positives. Compare cases with and without the signal.
Watch for issuer coverage. A trust signal only helps if enough of your users have a history with issuers you accept. Also check latency and failure handling. If the check fails, your flow should still make a deterministic decision.
That is the right design approach for any decision logic. The system should keep working when one input is missing.
Conclusion
Private State Tokens will not replace antifraud teams, and they will not replace underwriting policy. They do add a cleaner way to verify browser-level trust without leaning on invasive fingerprinting.
For lenders and ecommerce teams, the value is simple. Better signals. Less friction. More auditable decision logic.