Anti-fraud decision logic for consumer lending / BNPL
Published on: 2024-08-10 18:37:05
After eligibility checks, add anti-fraud decision rules to the same decision flow. In consumer lending and BNPL, cover Know Your Customer (KYC) checks plus volatility, velocity, and concentration signals.
Use four rule categories:
- Veracity Rules
- Volatility Rules
- Velocity Rules
- Concentration & Networking Rules
Veracity Rules
KYC rules validate submitted data against authoritative sources, such as a national identity database. If your market does not have automated access, verify the data through cross-checks and document analysis.
Cross-check core personally identifiable information (PII):
- Full name
- Address
- Employment
- Date and place of birth
- Identification card number
Verify PII against identity documents. Validate the address with alternative data such as delivery history, utility records, or geolocation consistency.
Cross-check the identification card number against stolen document lists and other relevant blocklists. Apply format rules, issuing authority checks, and expiry validation where available.
Also evaluate these signals:
- Social network profiles
- Phone number
- Email address
- IP address
- Bank account number
- Credit card number
Volatility Rules
Volatility is the difference between previously observed data and the current application. Data sources include your historical portfolio, credit bureaus, and alternative data providers. Some changes are normal, such as a recent job change. Others are signals, such as multiple addresses in a short period.
High volatility can indicate the use of stolen or synthetic identity elements that look plausible but do not persist. Examples include a new mobile number, a first-seen email domain, or a recently opened bank account with no prior activity.
Velocity Rules
Velocity measures how many applications appear for the same identity within a time window. Compute velocity across identity attributes such as address, employer, phone number, email, device ID, IP, bank account, or card number. Fraud rings reuse the same attributes across multiple applications. Include time-aware rules such as
- first seen
- last seen
- average interval between sightings
Concentration and Networking Rules
Concentration and networking rules limit risk from fraud clusters in one location or across connected identities. Concentration can signal an exploited loophole followed by a rapid rise in submitted cases. If left unchecked, it can create a fraud bubble that harms portfolio performance.
Reduce concentration using geolocation controls, sometimes called geofencing in fintech. Set thresholds by region, branch, merchant, or delivery point, and trigger step-up verification when caps are breached.
Networking rules rely on graph analysis with edges built from shared attributes. Useful edges include addresses, phone numbers, IP addresses, device IDs, and funding accounts.
Example rules:
- number of loans defaulted within the nth degree
- number of loans defaulted from the same region
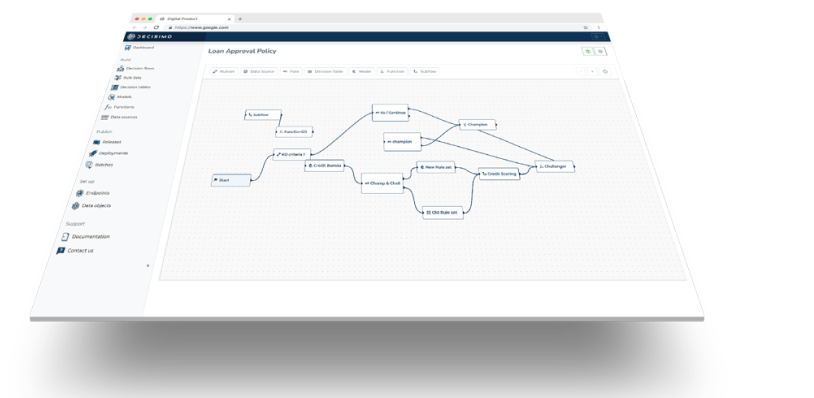
Implement these rules as decision tables and rulesets in your decision logic. Orchestrate external APIs for KYC, device, and geodata checks. Log decision traces so every evaluation is explainable and auditable.