Antifraud investigation in lending: how to detect, trace, and validate risk
Published on: 2026-04-04 15:13:49
Why antifraud investigation matters in lending
Lending teams do not lose money only when fraud gets approved. They also lose time, trust, and control when they cannot explain what happened, how far it spread, and which cases need action now. That is why antifraud investigation belongs in the decision process, not as a separate cleanup task.
In practice, investigation answers three questions: Is this real fraud? How large is the exposure? What should we do with the related cases? Those questions matter in consumer lending, SME lending, and payment-linked credit products. They also matter when the first signal is weak. For example, a sharp rise in one merchant, one product, one city, or one provider can be the first visible sign of a wider fraud ring.
A good process helps teams move from suspicion to evidence. It also creates traceability. Every step, from trigger to conclusion, should be auditable.
The two core investigation paths
Most antifraud work in lending falls into two areas. The first is backoffice, data-driven investigation. The second is field investigation. They solve different problems, and both are necessary.
1. Backoffice, data-driven investigation
This is the analytical side. Analysts review application data, device data, transaction data, repayment behavior, and relationship data. The goal is to find connections that are not visible in a single case view.
Teams look for shared attributes across applications and accounts. That includes the same phone numbers, devices, IP ranges, merchants, addresses, business names, directors, or support contacts. They also look for patterns in time. A fraud case often expands in bursts, then settles once a control is added or a channel is blocked.
Graph analysis is useful here. It shows related entities and helps teams see the scope of a case. A single suspicious application may connect to dozens of others through one device, one IP provider, or one registered address. The graph does not prove fraud on its own. It does show where to investigate next.
2. Field investigation
Field investigation checks whether the real-world story matches the data. In consumer lending, that may mean validating addresses or calling contact numbers. In SME lending, it can mean checking whether the business exists at the stated location, whether staff are present, and whether the business activity matches the application.
It can also include mystery shopping, support-line checks, and review of related businesses. If multiple entities claim different operations but share the same address, the same people, or the same contact path, the investigation needs to go deeper.
Field work is slower than data review, but it is often decisive. It confirms whether a cluster is a genuine customer segment or a synthetic one.
What triggers an antifraud investigation
Investigations usually start with a trigger. Good teams define triggers before the fraud case grows. That shortens response time and keeps work focused.
- Sudden volume increases in applications, approvals, or payments.
- Concentration changes in a segment, merchant, product, city, or region.
- Shorter behavior cycles across entities, such as fast repeat use or rapid account creation.
- Device concentration shifts in application traffic.
- IP address or provider concentration changes that indicate orchestration or automation.
- Repayment anomalies that do not match the expected portfolio profile.
In payment fraud, a sudden rise in device reuse or a new IP provider cluster can point to coordinated activity. In lending, a sharp increase in one city or one product can mean the fraud is moving through a specific channel. In SME lending, repeated links between businesses, directors, and contact details can expose organized application fraud.
The key is not to wait for losses. The point of early warning is to investigate before the pattern becomes expensive.
Early warning investigation: what to look for first
Early warning investigation starts with pattern detection. Analysts compare current behavior against baseline behavior. They ask what changed, when it changed, and whether the change is isolated or connected.
Useful questions include:
- Which segment changed first?
- Is the growth linked to one channel, one merchant, or one region?
- Are the same devices, addresses, or IP ranges appearing across many cases?
- Do the applications share similar wording, timing, or document patterns?
- Are related entities appearing faster than usual?
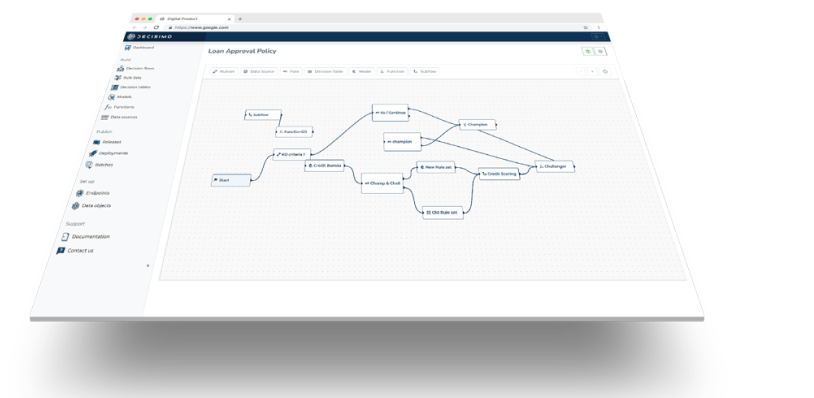
This is where decision logic matters. The platform should evaluate triggers consistently, log the result, and preserve the rule version used at the time. That makes the investigation explainable later.
If you want a broader view of how decision systems support this kind of work, see What is a decision engine? and 5 Important Components of Rule Engine Architecture.
How data-driven investigation exposes scope and scale
A fraud case is rarely limited to the first suspicious record. The real work is figuring out how far it spreads. That is why investigators map entities and relationships.
Start with the known suspicious case. Then expand outward through shared identifiers and shared behavior. Common link types include:
- Devices
- IP addresses
- Phone numbers
- Email addresses
- Physical addresses
- Company directors
- Beneficial owners
- Bank accounts
- Merchants
- Support contacts
When the graph shows several applications tied to the same hidden cluster, the case scope is larger than the original signal. That can change the response. One isolated case may lead to a manual review. A connected cluster may justify rule updates, channel restrictions, or a broader portfolio review.
This approach is similar to what lenders do when they monitor risk at portfolio level. For a related view, read Portfolio Management in Lending: What Matters Most and Metrics to Monitor in Lending and Credit Underwriting.
Field investigation: validating the real-world story
Data can show a pattern. Field investigation shows whether the pattern is real.
In consumer lending, an investigator may call a listed number, check whether the address exists, or verify whether the stated employer is active. In SME lending, the work is broader. Teams may visit the business address, inspect signs of operation, check whether the company has visible activity, and confirm whether the business type matches the application.
Field teams often look for related businesses too. If one address hosts multiple legal entities, the investigator should ask why. If several companies share staff, phones, or bank accounts, the relationship needs to be explained. Sometimes there is a valid operating structure. Sometimes there is a fraud ring using a network of shell entities.
Mystery shopping can be useful when the applicant claims a customer-facing operation. A quick visit or call can confirm whether the business behaves like the application says it does. That is especially useful when the fraud signal is about merchant quality, fake storefronts, or misrepresented activity.
How investigation changes the lending decision
Investigation is not only about closing a case. It should feed back into the lending flow.
When the case is confirmed, teams can:
- Block linked entities.
- Update decision rules.
- Raise review thresholds for affected segments.
- Escalate suspicious clusters to compliance or risk teams.
- Preserve evidence for audit and dispute handling.
When the case is inconclusive, teams can still reduce risk. They may add a monitoring rule, request stronger verification, or narrow approval until the pattern is clear.
That feedback loop is the point. Fraud investigation should improve decision logic, not just document losses.
Building a process that works under pressure
A useful antifraud process is simple to describe and strict in execution.
- Detect a trigger from volume, concentration, or behavior shifts.
- Open the case with the first evidence and the baseline comparison.
- Expand the data review through entity links and graph analysis.
- Validate the field facts where the case requires real-world checks.
- Decide the response based on scope, confidence, and exposure.
- Feed the result back into rules, monitoring, and portfolio controls.
That process works because it separates signal detection, case sizing, and physical validation. It avoids the common mistake of treating every suspicious case the same way.
What good teams do differently
Good teams do not wait for fraud losses to define their process. They define triggers, routes, and ownership in advance. They know which cases need data review, which need field checks, and which need both.
They also keep the decision path explainable. Every case should show why it was flagged, which entities were linked, what changed in the baseline, and what was found during field validation.
That is important in lending because fraud controls affect growth. If the process is slow or unclear, teams approve too much risk or block too many good customers. If the process is structured, they can respond faster and with less noise.
Final point
Antifraud investigation is not a back-office afterthought. It is part of lending control. The work starts with a trigger, expands through data, and ends with validation in the real world when needed. Done well, it shows the scope of the case early, reduces avoidable losses, and improves the decision logic that sits upstream.
For teams building or refining their investigation flow, the core rule is simple: do not rely on one signal. Combine graph-based analysis, early warning triggers, and field validation, then record the outcome in a way the business can audit.